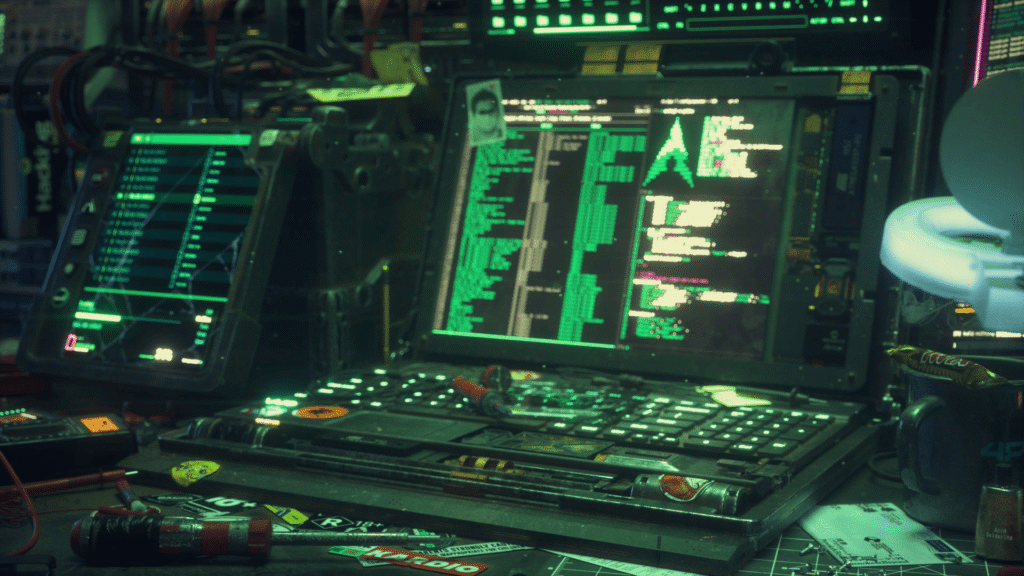
🔒 Educational Security Research Toolkit | For authorized testing only
A modular CLI framework for authorized web application security assessments and defensive research. Designed exclusively for penetration testers, red teamers, and security researchers operating under explicit written authorization.
⚠️ LEGAL DISCLAIMER (READ BEFORE USE)
THIS TOOL IS FOR EDUCATIONAL AND AUTHORIZED SECURITY TESTING ONLY.
- ✅ LEGAL USE: Systems you own OR systems where you have written authorization (signed contract/engagement letter).
- ❌ ILLEGAL USE: Any system without explicit permission violates:
- Computer Fraud and Abuse Act (CFAA – USA)
- GDPR Article 32 (EU)
- Ecuadorian Organic Law on Telecommunications (Art. 132)
- Similar laws in 180+ countries
You are solely responsible for your actions.
Spectre Daemon Industries and contributors assume zero liability for misuse. Unauthorized access to computer systems is a criminal offense punishable by fines and imprisonment.
🔐 Ethical Principle: “With great power comes great responsibility.” — Never test what you don’t own or aren’t explicitly authorized to test.
📌 Purpose & Scope
This framework provides reconnaissance and assessment modules for:
- Web server fingerprinting (
whatweb,nmap) - Directory brute-forcing (
gobuster) - Header analysis
- Report generation
⚠️ Important:
Modules labeled “stealth” or “evasion” demonstrate defensive research concepts for blue teams to understand attack patterns. They are not guaranteed to bypass modern security systems and should never be used against production systems without authorization.
⚙️ Requirements
# Kali Linux / Parrot OS (recommended)
sudo apt install -y curl nmap whatweb sqlmap gobuster hydra netcat tor
# Directory setup
mkdir -p ~/Autom🚀 Usage
git clone https://github.com/spectredaemon/spectre-daemon-framework.git
cd spectre-daemon-framework
chmod +x spectre-daemon.sh
# ⚠️ ONLY RUN AGAINST SYSTEMS YOU OWN OR HAVE WRITTEN AUTHORIZATION FOR
./spectre-daemon.sh